SpiderFoot automates OSINT so you can focus on analysis.
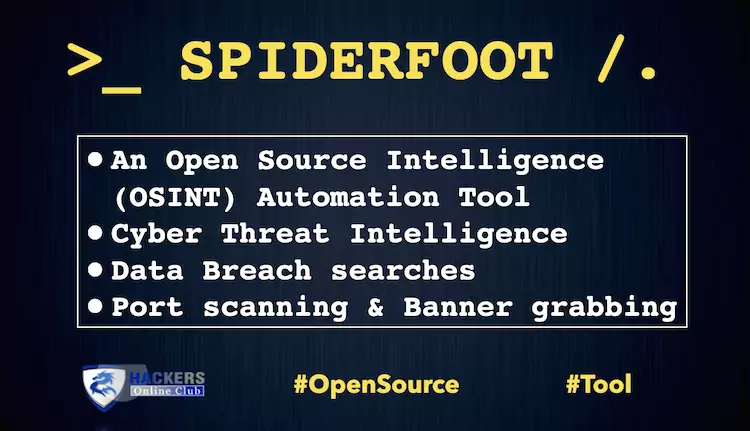
SpiderFoot is an open source intelligence (OSINT) automation tool. It integrates with just about every data source available and utilises a range of methods for data analysis, making that data easy to navigate.
SpiderFoot is a reconnaissance software that automatically queries over 100 public data sources (OSINT) to gather intelligence on IP addresses, domain names, e-mail addresses, names and more.
You simply specify the target you want to investigate, pick which modules to enable and then SpiderFoot will collect data to build up an understanding of all the entities and how they relate to each other.
SpiderFoot has an embedded web-server for providing a clean and intuitive web-based interface but can also be used completely via the command-line. It’s written in Python 3 and GPL-licensed.
FEATURES
- Web based UI or CLI
- Over 200 modules (see below)
- Python 3
- CSV/JSON/GEXF export
- API key export/import
- SQLite back-end for custom querying
- Highly configurable
- Fully documented
- Visualisations
- TOR integration for dark web searching
- Dockerfile for Docker-based deployments
- Can call other tools like DNSTwist, Whatweb, Nmap and CMSeeK
Also See: Oblivion – Data Leak Checker And OSINT Suite
WANT MORE?
Need more from SpiderFoot? Check out SpiderFoot HX for:
- 100% Cloud-based and managed for you
- Attack Surface Monitoring with change notifications by email, REST and Slack
- Multiple targets per scan
- Multi-user collaboration
- Authenticated and 2FA
- Correlations
- Investigations
- Customer support
- Third party tools pre-installed & configured
- Drive it with a fully RESTful API
- TOR integration built-in
- Screenshotting
- Feed scan data to Splunk, ElasticSearch and REST endpoints
- See the full set of differences between SpiderFoot HX and the open source version here.
USES
SpiderFoot can be used offensively (e.g. in a red team exercise or penetration test) for reconnaissance of your target or defensively to gather information about what you or your organisation might have exposed over the Internet.
You can target the following entities in a SpiderFoot scan:
- IP address
- Domain/sub-domain name
- Hostname
- Network subnet (CIDR)
- ASN
- E-mail address
- Phone number
- Username
- Person’s name
- Bitcoin address
SpiderFoot’s 200+ modules feed each other in a publisher/subscriber model to ensure maximum data extraction to do things like:
- Host/sub-domain/TLD enumeration/extraction
- Email address, phone number and human name extraction
- Bitcoin and Ethereum address extraction
- Check for susceptibility to sub-domain hijacking
- DNS zone transfers
- Threat intelligence and Blacklist queries
- API integration with SHODAN, HaveIBeenPwned, GreyNoise, AlienVault, SecurityTrails, etc.
- Social media account enumeration
- S3/Azure/Digitalocean bucket enumeration/scraping
- IP geo-location
- Web scraping, web content analysis
- Image, document and binary file meta data analysis
- Dark web searches
- Port scanning and banner grabbing
- Data breach searches
INSTALLING & RUNNING
To install and run SpiderFoot, you need at least Python 3.7 and a number of Python libraries which you can install with pip. We recommend you install a packaged release since master will often have bleeding edge features and modules that aren’t fully tested.
Stable build (packaged release):
$ wget https://github.com/smicallef/spiderfoot/archive/v3.4.tar.gz
$ tar zxvf v3.4.tar.gz
$ cd spiderfoot
$ pip3 install -r requirements.txt
$ python3 ./sf.py -l 127.0.0.1:5001
Development build (cloning git master branch):
$ git clone https://github.com/smicallef/spiderfoot.git $ cd spiderfoot $ pip3 install -r requirements.txt $ python3 ./sf.py -l 127.0.0.1:5001
COMMUNITY
Whether you’re a contributor, user or just curious about SpiderFoot and OSINT in general, we’d love to have you join our community! SpiderFoot now has a Discord server for chat, and a Discourse server to serve as a more permanent knowledge base.
MODULES / INTEGRATIONS
SpiderFoot has over 200 modules, most of which don’t require API keys, and many of those that do require API keys have a free tier.