Browsing Category
Server
112 posts
PassKeys – Apple New Generation Password Authentication
Apple’s PassKeys – A New Generation Password Authentication. Using passkeys for account authentication is far simpler and more secure…
September 7, 2022
Host Based Intrusion Detection System HIDS
Host based intrusion detection systems (HIDS) detect and prevent malicious attacks on computers. It works similarly to a…
July 29, 2022
Proxy or VPN – What To Choose?
With the global development of the internet, there are more and more sites where we leave our sensitive…
July 22, 2022
Microsoft Zero-Day Vulnerability Found In MS Office Suite
A newly discovered Microsoft zero-day vulnerability in its Office productivity suite could be exploited to deliver remote code…
May 31, 2022
7 Tips For Secure Web Data Extraction
Web data extraction, often known as web scraping, involves gathering data online through bots and other programs that…
May 12, 2022
Secret Keys Found in Samsung Source Code Leaked Online
A hacker group leaked Samsung and Nvidia’s source code online, according to reports. Previously, many vulnerabilities have been…
March 15, 2022
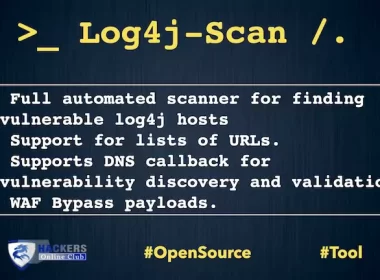
Log4j Scanner Automated Open Source Software
log4j-scan is a fully automated, accurate, and extensive scanner for finding vulnerable log4j hosts. A part of the Apache…
December 22, 2021
What is Apache Log4j – Security Vulnerability Fixes
Apache Log4j vulnerability highlighted by security researchers last Friday: Experts say it could lead to sensitive data leakage.…
December 16, 2021
Acra Database Security Suite With Field Level Encryption And Intrusion Detection
Acra open-source Database Security suite with field level encryption and intrusion detection system. Database proxy with field-level encryption,…
December 3, 2021
New Banking Malware Program NOMANDO Targets Latin America
The ESET security researchers found a new banking malware program named "Nomando“. Nomando, written in Delphi, uses fake…
September 20, 2021