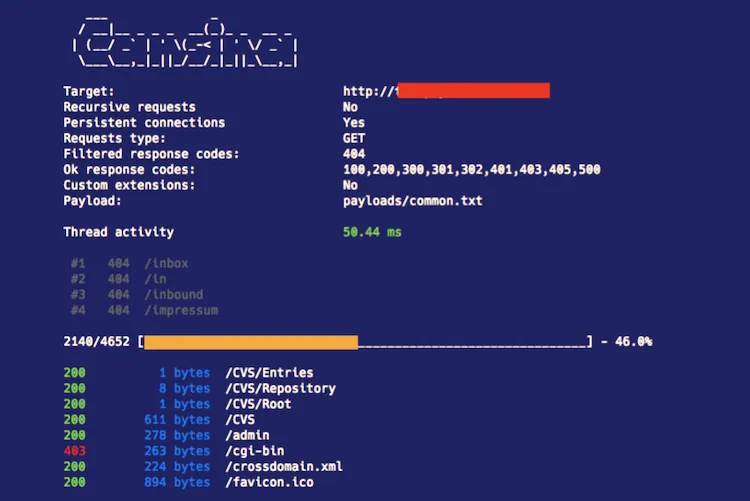
It is well known Web applications don’t publish all their resources or public links, so the only way to discover these resources is requesting for them and check the response.
Cansina duty is to help you making requests and filtering and inspecting the responses to tell apart if it is an existing resource or just an annoying or disguised 404.
Cansina is included in BlackArch Linux, give it a try!
Installation
pip install cansinaIf you don’t want to pollute your environment to try cansina just create a virtual env
Usage
Wiki is full of documentation and examples. But as a fast example:
cansina -u -pHelp summary:
cansina -hFeatures
- Data persistence with sqlite database
- Optional output in CSV format
- Multithreading
- Multiextension
- Custom headers
- Multiple wordlists from directories
- Content detection
- Filter results by size
- Filter results by content
- URL pattern (***) to interpolate strings
- SSL support
- Proxy support
- Basic Authentication
- Cookie jar
- Resuming
- Path recursion
- Persistent connections
- Complementary tools
Speed
Wanna make Cansina run faster?
Cansina downloads page content for inspection by default (Yep, Cansina does not racing for speed). but you can disable GET requests and make them HEAD (no body page download). Also, do no print the fancy terminal interface (you will lost some hackish points).
- Put -H to make requests lighter
Put –no-progress to print no fancy information in the screen
Raise default threads to ten with -t 10 (or even more if you don’t mind noise and faulty tries)
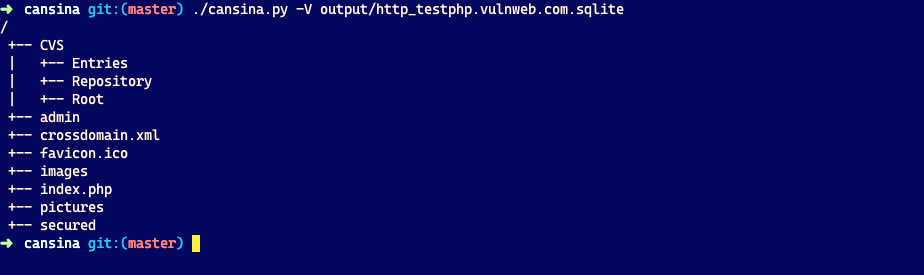
Integrated tree viewer
Cansina integrates a tree viewer (thanks to asciitree package) to output a project sqlite base stored results (http 200 status code by now).
cansina -V output/http_testphp.vulnweb.com.sqlite
Important
This tool is intended to be used in a fair and legal context, meaning, for example, a penetration testing for which you have been provided previous authorization.
One of its legitimate uses might be the one described in the following article:
Dependencies
Windows
Untested in Windows. It should work with –no-progress