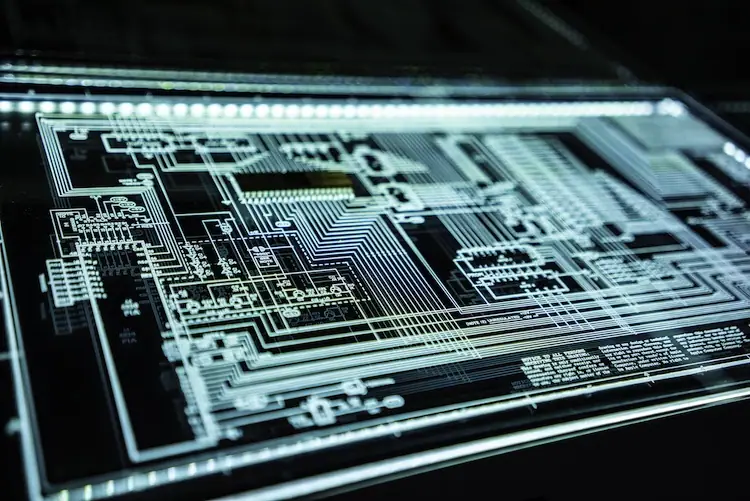
IEC 62443 is a set of standards for digital security set by the International Electrotechnical Commission (IEC) to address vulnerabilities and threats affecting industrial automation and control systems. It provides comprehensive guidelines covering technical and process-related areas of securing operational technology and automation.
Approved by the IEC in 2021, this is a relatively new set of standards. It is understandable why many find it challenging to adopt it into their existing systems. Not many are even aware if the standards apply to the nature of their operations.
The Global Cybersecurity Alliance (GSA) offers a practical guide for IEC 62443 adoption but it is focused on industrial control systems (ICS). Presented below is a simplified enterprise security counterpart of what the GSA recommends, with an emphasis on skills training.
Funding and skill challenges
Two major obstacles hamper the seamless adoption of IEC 62443 and other security standards: funding and skills, or the lack thereof. The implementation of new rules and processes requires technical and procedural adjustments as well as system upgrades that entail added costs. Some companies turn to third-party consulting or support services to help them proceed efficiently, and this also means additional expenses.
Even though more organizations already consider security as the top IT funding priority according to one study on enterprise funding priorities, IEC 62443 may not be the kind of priority businesses are anticipating. Manufacturers of IoT devices, for example, may not have the financial readiness and technical proficiency to implement the standards effectively on their own.
On the other hand, the skills factor is a vital concern. The cybersecurity professionals in an organization may not be that receptive to changes, especially since many of them tend to be overworked. Cybersecurity skills shortage continues to be a problem worldwide. Requiring them to upskill and familiarize new concepts may not be that easy. Also, making automation engineers and IoT developers learn and work with IEC 62443 will be a challenge, given that security is conventionally not part of their job.
Implementing IEC 62443 based on GSA recommendations
The Global Security Alliance’s suggestions on the implementation of IEC 62443 has a number of stages, which can be reinterpreted for enterprise security application, as summarized below.
- Assessment of current systems and the definition of the scope of the implementation. Enterprises need to comprehensively examine their existing systems and identify areas that need improvement to meet the standards.: Based on the assessment, organizations should define the scope of the integration project, including the systems and processes that will be impacted.
- Plan development. To avoid unnecessary steps and costs, it is crucial to come up with a detailed plan. This should include timelines, budgets, and resource allocation.
- Personnel training. Training employees on how to implement IEC 62443 is a crucial part of the process. Everyone should know what their roles are. It is also important for the management to support everyone toward the effective fulfillment of their responsibilities.
- Phased implementation. GSA advises that the implementation of the standards should follow a phased approach. Areas of focus and priorities should be set to proceed efficiently.
- Testing and validation. New security standards adoption does not stop with the implementation. It is important to test and validate the new system with IEC 62443 integrated to make sure that everything works as intended.
- Monitoring and maintenance. To achieve the best outcomes, organizations should continuously monitor and maintain the systems and processes to ensure they remain in compliance with the IEC 62443 standards.
These may look simple and straightforward, but the process can be lengthy and tedious. Things can get complicated without a thorough understanding of what the standards require and what they are supposed to achieve. This is why some enterprises resort to using consultancy or support services.
Overcoming the challenges
The costs of implementing new security standards are inevitable. The best organizations can do is to rationalize spending and plan everything strategically to avoid wasteful expenditures and maximize the benefits. The best way to overcome the cost challenge is to achieve undeniable ROI at the soonest possible time.
It would not be unusual if the management and stakeholders show resistance against adopting new security standards. That’s why it is the responsibility of the cybersecurity team or the IT department, in general, to put out compelling arguments to push for the implementation of IEC 62443. They have to advocate for it, lest they fail to achieve the expected outcomes because of tepid efforts and inadequate management support.
One of the best arguments the IT team can use is the emergence of new laws or regulations requiring the improved security of operational technology and IoT. In the United States, for example, there is a plan to establish an IoT labeling system, which forces IoT manufacturers to secure the devices they offer throughout the product development lifecycle. Adopting the IEC 62443 standards benefits the process of securing IoT products.
When it comes to skills shortage, it helps to understand the difficulties encountered by those who will be directly involved with the IEC 62443 implementation. Many of them likely do not have the time for the training or are unmotivated because of their workload. The expectation is that organizations should hire more cybersecurity professionals to address new security concerns.
GSA, however, suggests that cybersecurity professionals and others who are expected to learn IEC 62443 do not necessarily dread the idea of learning and applying new security standards. Organizations that are grappling with limited resources can ingenuously facilitate training and provide the support the standards implementation needs.
Cybersecurity professionals are accustomed to learning technical skills. Even automation engineers whose job descriptions do not include cybersecurity can easily participate in a new security standards implementation with the right strategies. To ensure fast and effective upskilling, it is important to develop a suitable training program or course.
Providing proper training
The right IEC 62443 training program has to focus on the seven core functional requirements, namely identification and authentication, use regulation, system integrity, data confidentiality, data flow restriction, timely event/incident response, and resource availability. “These seven areas are easy to train,” notes GCA in a blog post on how to better train engineers in IEC 62443.
A training program that sufficiently covers these topics is an excellent first step toward successful IEC 62443 implementation. The program has to be as concise as possible and packed with all the important details. The content of the training course depends on the specific needs of an organization, but it usually includes the following: patch management, backup management, endpoint protection, network security, and log management.
In summary
Not many organizations have enough funding and skills to adopt a new security standard. These limitations are not enough reason to ignore security standards, though. Enterprises engaged in the operation or manufacture of ICS and IoT systems need to be resourceful and creative in adopting IEC 62443 to ensure optimal security.