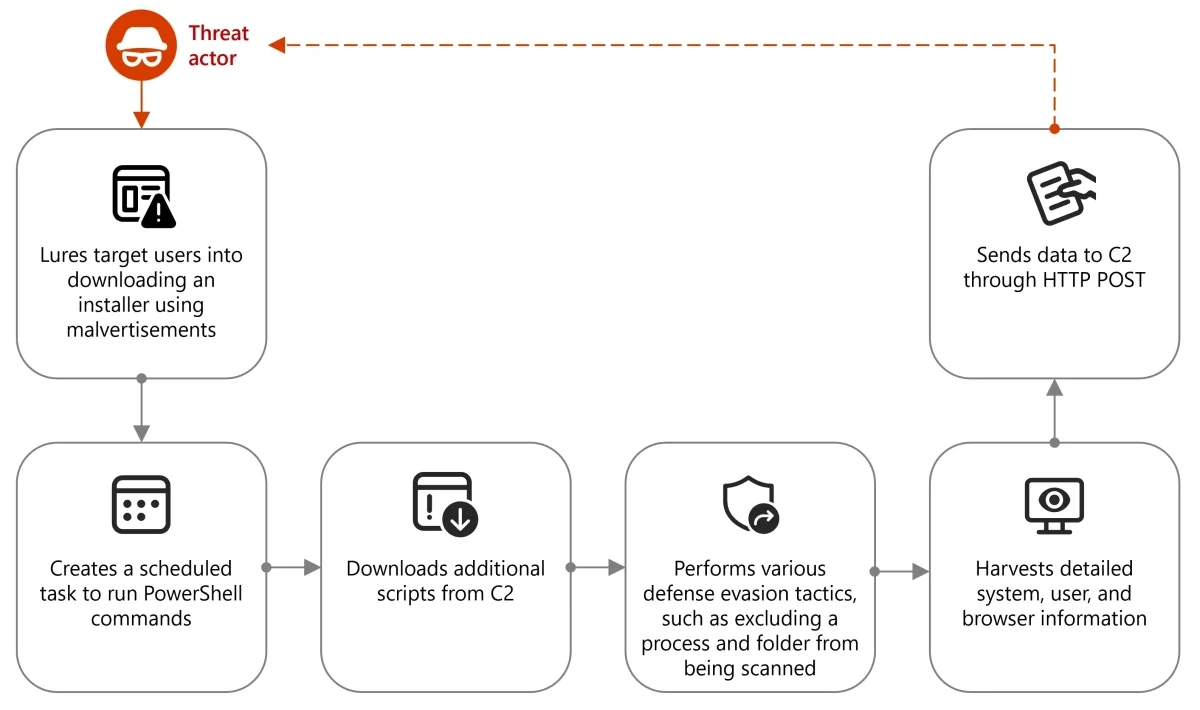
Microsoft has issued a warning about threat actors increasingly misusing Node.js to deliver malware and malicious payloads, leading to information theft and data exfiltration. According to a recent Microsoft Security, Microsoft Defender Experts (DEX) have observed campaigns since October 2024 where attackers are leveraging Node.js to blend malware with legitimate applications and bypass security controls.
Key Findings:
- Malvertising Campaigns: Attackers are using malvertising to lure targets to fraudulent websites, where they unknowingly download malicious installers disguised as legitimate software.
- Malicious Installers: These installers contain malicious DLLs that gather system information and set up scheduled tasks for persistence.
- Inline JavaScript Execution: Attackers are deploying malware directly through Node.js using techniques like inline JavaScript execution.
- Disguised Command-and-Control Traffic: Attackers are disguising command-and-control traffic as legitimate Cloudflare activity.
Data collection and exfiltration
With the exclusions set, an obfuscated PowerShell command is then launched through scheduled tasks to continuously fetch and run scripts from remote URLs. These scripts gather detailed system information, including:
- Windows information: Registered owner, system root, installed software, email addresses
- BIOS information: Manufacturer, name, release date, version
- System information: Name, domain, manufacturer, model, domain membership, memory, logical processors, graphics processing units (GPUs), processors, network adapters
- Operating system information: Name, version, locale, user access control (UAC) settings, country, language, time zone, install date
Microsoft’s Recommendations:
To mitigate these threats, Microsoft recommends the following:
Educate users about the risks of downloading software from unverified sources.
- Monitor Node.js execution.
- Enforce PowerShell logging.
- Use endpoint protection solutions.
- Turn on cloud-delivered protection.
- Run EDR in block mode.
- Use PowerShell’s execution policies.
This report highlights the evolving tactics of cybercriminals and the importance of staying vigilant against new attack vectors. Microsoft’s recommendations provide actionable steps for organizations to strengthen their defenses against these emerging threats.