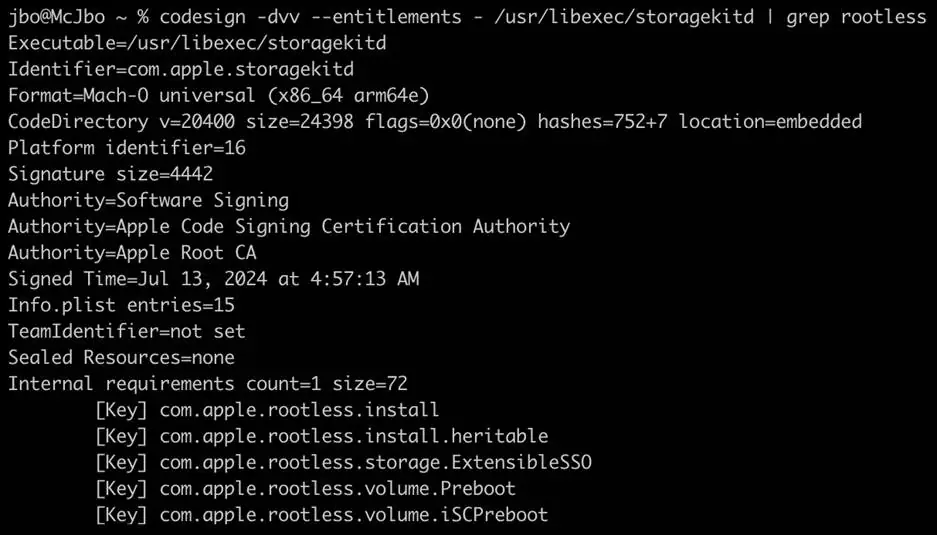
A recently patched macOS vulnerability, designated as CVE-2024-44243, has shed light on the importance of timely software updates and collaboration within the tech industry to ensure system security. Discovered by Microsoft Threat Intelligence, this critical flaw threatened the core security mechanisms of Apple’s operating system.
The connection between entitlements and SIP and explain how CVE-2024-44243 could be used to bypass SIP security measures. This research also highlights some of the benefits and challenges of kernel-based monitoring, said in the Microsoft blog.
Prohibiting third party code to run in the kernel can increase macOS reliability, the tradeoff being that it reduces monitoring capabilities for security solutions. If SIP is bypassed, the entire operating system can no longer be considered reliable, and with reduced monitoring visibility, threat actors can tamper with any security solutions on the device to evade detection.
What is CVE-2024-44243?
CVE-2024-44243 is a vulnerability that allowed attackers to bypass a fundamental macOS security feature known as System Integrity Protection (SIP). SIP restricts unauthorized modifications to critical system components, safeguarding the operating system’s integrity. By exploiting CVE-2024-44243, attackers could have gained the ability to:
- Install persistent malware: Malicious actors could have deployed undetectable malware that would survive typical removal attempts, posing a long-term threat to the system’s security.
- Compromise system integrity: With SIP bypassed, attackers could have altered core system files and configurations, potentially destabilizing the operating system.
- Evade detection: Bypassing SIP could have allowed malware to cloak its activities from traditional security measures.
Impact of CVE-2024-44243
A successful exploit of CVE-2024-44243 could have had severe consequences for macOS users. The ability to bypass SIP would have opened the door to a range of malicious activities, potentially compromising sensitive data, disrupting system functionality, and rendering traditional security solutions ineffective.
Patch Availability and Mitigation
Fortunately, Apple addressed CVE-2024-44243 in macOS Sequoia 15.2, released in December 2024. Users are strongly advised to update their macOS systems to the latest version to ensure they are protected from this vulnerability.
Key Takeaways
- CVE-2024-44243 highlights the critical role of SIP in safeguarding macOS systems.
- Timely software updates are essential to maintaining system security and patching vulnerabilities.
- Collaboration between tech companies is vital for identifying and resolving security threats.