Routers are important device that provides Internet.
A router is a networking device that forwards data packets between computer networks. Routers perform the traffic directing functions on the Internet. Data sent through the internet, such as a web page or email, is in the form of data packets. A packet is typically forwarded from one router to another router through the networks that constitute an inter-network until it reaches its destination node.
In Brazil, 88 percent of router is infected in the malicious campaign, the security researchers are found 100k+ infected router IP Address and 70+ router/firmware have been involved and 50+ domain names including big Banks, Netflix has been hijacked to steal the website login credentials.
The campaign first spotted by Radware since mid-August. In Radware Threat Research Center has identified a hijacking campaign aimed at Brazilian Bank customers through their IoT devices, attempting to gain their bank credentials.
According to the Netlab report, the security experts expose more details in the research. The hackers are scanning the Brazilian IP Space for routers that use no weak or no passwords, accessing the routers settings and replacing legitimate DNS setting with the IP’s of DNS servers under their control.
What is DNSChanger?
DNSChanger is a type of Malware used by hackers to change a users DNS Server settings and replacing with rogue DNS servers operated by Cyber attacker.
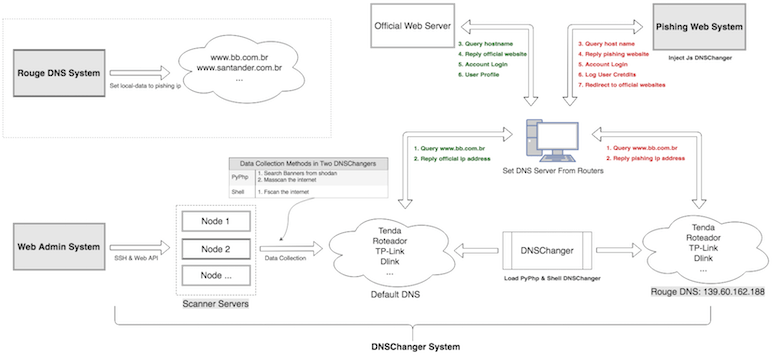
DNSChanger is the main module of GhostDNS. The cyber attacker can use three DNSChanger sub-modules to carry out an attack against routers on both internet and intranet networks. The module includes 100+ attack scripts together, affecting 70+ different routers.
Netlab found three DNSChanger program module with Shell DNSChanger, JS DNSChanger and PyPhp DNSChanger according to their programming languages. These DNSChanger systems are only part for run Malware campaign.
More campaign including Phishing Web System, Web Admin System, Rogue DNS System are also parts work together to perform DNS Hijacking function, and its called GhostDNS.
The cyber attack happens in three different modules.
The First module is shell DNSChanger-
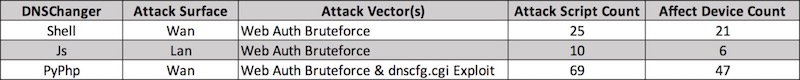
It is written in shell and a combination of 25 attack shell scripts that can brute-force the passwords of 21 routers of firmware packages.
This sub-module is only being used lightly with limited deployment by the attacker and uses the FScan program to perform. Fscan is using IP range list of targeted networks.
The Second Module is JS Changer-
It is written in JavaScript and collection of 10 JS scripts that can infect the 6 routers of firmware packages.
It is mainly divided into scanners, to generate payloads and attack programs.
The Third Module is PyPHP DNSChanger-
It is written in the combination of Python and PHP. It is a most important module, it has been deployed on over 100 Google cloud servers from where the attackers are constantly scanning the internet to identify vulnerable routers.
The module uses 69 attacks scripts that can brute-force the passwords of 47 different routers and firmware packages.
Web Admin System
Netlab also discovered a web admin website on one of the PyPHP DNSChanger nodes and found one of the admin systems.
Infected Routers Statics
On the basis of GhostDNS logs from 21Sep- 27Sep, Netlab observed that 100k+infected router IP address including 88 percent in Brazil, with 70+routers/firmware. Due to the dynamic updates of the router IP address, the actual number of an infected device should be slightly different.
How to Protect your routers?
- Always keep updating your routers
- Change router login and password regularly
- USE WPA2 to secure your Wireless network
- Use Better DNS Service











